All federal and DoD contracts issued since 2016 require safeguarding protected government information, including Federal Contract Information (FCI) and Covered Defense Information (CDI), including Controlled Unclassified Information (CUI).
Cloud service providers used by federal contractors must meet the Federal Risk and Authorization Management Program (FedRAMP) standard.
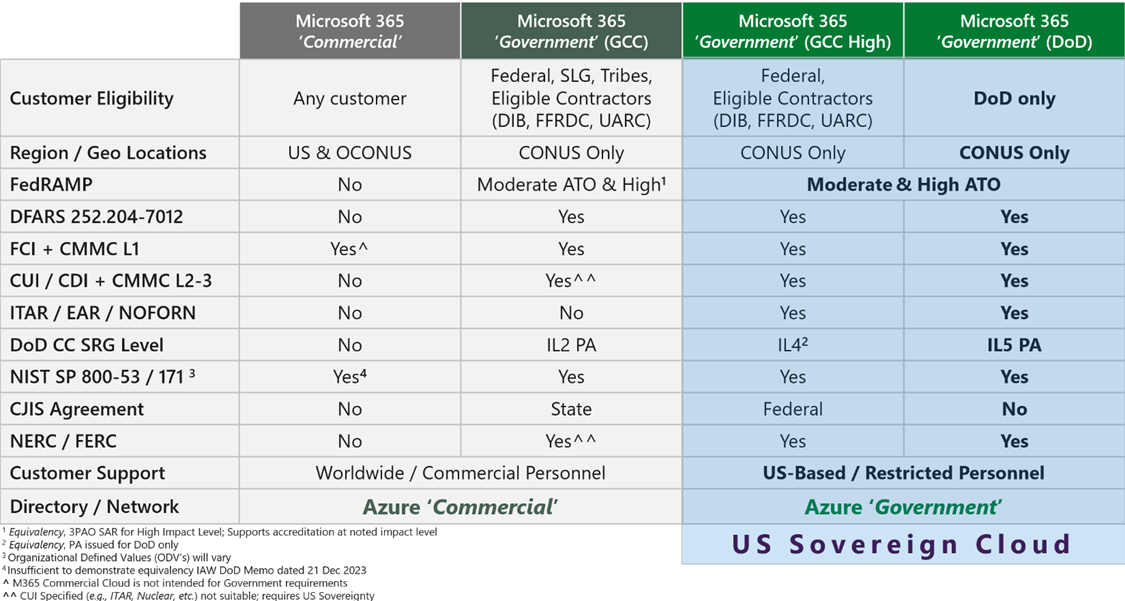
Microsoft 365 Commercial does not meet FedRAMP standards and cannot be used to store, process, or transmit any protected government information, including contract details such as delivery timelines, costs, or statements of work.
Using Microsoft 365 Commercial is not in compliance with contractual obligations and may trigger False Claims Act violations.
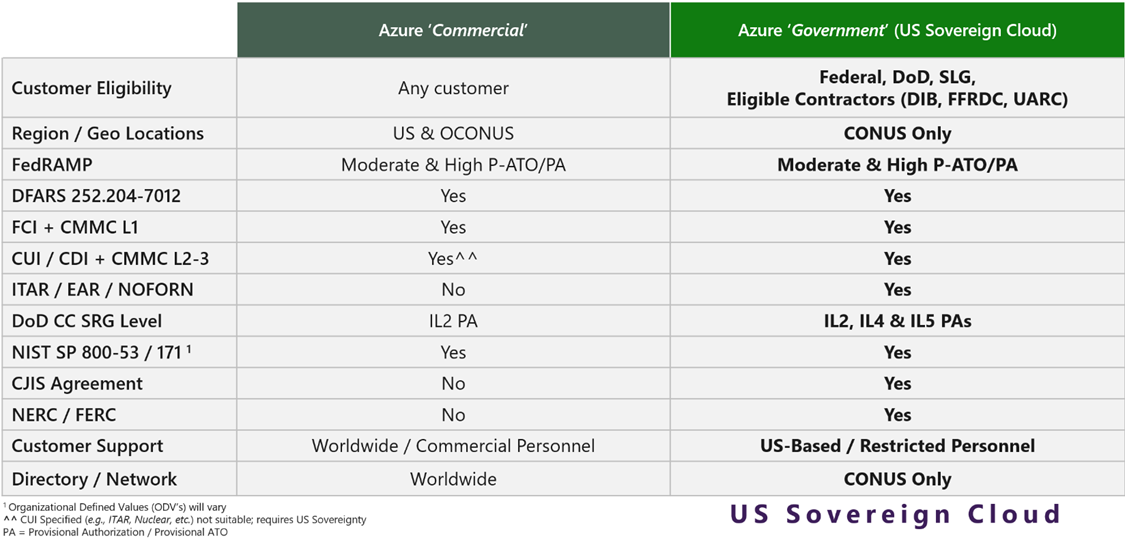
Microsoft Azure Commercial routes support requests, including cybersecurity incident response, to global support staff rather than to US citizens located in United States data centers, as required by regulations.
Using Microsoft Azure Commercial does not meet cybersecurity reporting requirements in all situations and can result in False Claims Act violations.
All federal contracts since 2016 include FAR 52.204-21 Basic Safeguarding of Covered Contractor Information Systems. This regulation outlines the basic cybersecurity requirements for contractors who store, process, or transmit Federal Contract Information (FCI). This regulation applies to all federal contractors, including those working with the Department of State or other non-defense government agencies.
All Department of Defense (DoD) contracts since 2016 include DFARS 252.204-7012 Safeguarding Covered Defense Information and Cyber Incident Reporting (DFARS 7012). This regulation outlines the basic cybersecurity requirements for contractors who store, process, or transmit Federal Contract Information (FCI) and Covered Defense Information (CDI), including Confidential Unclassified Information (CUI). The specific cybersecurity requirements are defined in NIST SP 800-171 Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations. When using Cloud Service Providers, the service must meet the FedRAMP Moderate baseline to be compliant with DFARS 7012.
Microsoft states that Azure Commercial meets the DFARS 7012 requirement, but qualifies that statement by noting that they cannot distinguish between commercial and government tenants in Azure Commercial. Microsoft Commercial support leverages a global follow-the-sun support model, routing support to the worldwide support team. DFARS 7012 sections c-g require that cybersecurity incident responses be handled by US citizens in the continental United States (CONUS). This cannot be guaranteed in Azure Commercial, which creates risk if an incident occurs.
The DFARS 7012 contract clause flows down, which requires all prime defense contractors to enforce the same safeguarding and reporting requirements for government information on its subcontractors that are imposed on the prime by their contract with the government. The implication is that any subcontractors who store, process, or transmit FCI/CDI/CUI must implement security controls from NIST SP 800-171 and report cyber incidents, even without a direct contract with the Department of Defense (DoD).
All contractors covered under DFARS 7012 are also directed to self-assess meeting the security requirements of NIST SP 800-171 and report their compliance in the Supplier Performance Risk System (SPRS). Knowingly reporting an inaccurate compliance score in SPRS can trigger a False Claims Act violation.
One key aspect of compliance with DFARS 7012 is to use Cloud Service Providers (CSP) who meet the required federal cybersecurity standards. The Federal Risk and Authorization Management Program (FedRAMP) is a United States federal government-wide compliance program that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services.
Microsoft 365 Commercial (now Office 365 Commercial) cloud services do not have FedRAMP authorization and are not compliant for government use. Microsoft provides a tool to identify the classification and scope of any cloud tenant.
https://gettenantpartitionweb.azurewebsites.net/
For example, searching for Lockheed Martin (lmco.com) using that tool displays the following information:
Tenant Name: lmco.com
Tenant GUID: b18f006c-b0fc-467d-b23a-a35b5695b5dc
Azure AD Instance: Azure AD Government: Arlington
Tenant Scope: GCC High
Note that the Tenant Scope will either be GCC or GCC High if the tenant is hosted on the government cloud.
Searching for Home Depot (homedepot.com) using that tool displays the following information:
Tenant Name: homedepot.com
Tenant GUID: fb7e6711-b619-4fbe-afe6-f83b12673323
Azure AD Instance: Azure AD Global: North America
Tenant Scope: Not applicable
When hosted on the commercial cloud, the Tenant Scope will be Not applicable. Note that the Azure AD Instance is listed as North America. This means their data may not be stored within the continental United States, which is required for some categories of protected government information.
The DoD created the Cybersecurity Model Cybersecurity Maturity Model Certification (CMMC) Program to provide compliance assistance and third-party assessments to verify contractors comply with DFARS 7012. The final rule for that program went into effect on December 15, 2024, and there is now a growing number of companies to assist contractors in meeting compliance and preparing for audits.
A new rule, DFARS 48 CFR Parts 204, 212, 217, and 252 Assessing Contractor Implementation of Cybersecurity Requirements, went into effect on November 10, 2025. All DoD contracts now will be able to specify the level of cybersecurity compliance to be eligible for award. The intention was to do a phased roll-out, which would allow contractors time to work toward compliance. It does not appear that will be the case.
On June 30, 2025, Lockheed Martin released a statement to their suppliers saying that “By now, all DIB companies managing CUI should have fully implemented – and be confidently meeting – NIST SP 800-171 (r2) requirements.” The message is that regardless of government actions, subcontractors must meet the requirements for working with large primes like Lockheed going forward.
None of these new CMMC programs and rules implement new requirements. They exist to verify that companies that self-report high SPRS scores to the government actually have the cybersecurity infrastructure to back them up. DoD contracts can now require cybersecurity compliance for award.
I recommend migrating from Microsoft 365 Commercial or Azure Commercial to Microsoft Government Computing Cloud (GCC) as soon as practical.
Depending on the reported SPRS scores, a review of compliance documentation should be performed in advance of an audit. An auditor will want to see:
A complete, up-to-date inventory of equipment and software licenses.
A diagram illustrating all key infrastructure, with a clear boundary indicating where FCI/CDI/CUI will be stored, processed, and transmitted.
A list of employees with their roles and responsibilities to guide limiting user access to only those resources required to perform their duties.
A corporate policy document from executives to staff to guide compliance.
A System Security Plan (SSP) to provide a high-level overview of how compliance obligations will be met.
A Shared Responsibility Matrix (SRM) showing how cybersecurity objectives are met and who is responsible for meeting them, such as internal staff or External Service Providers (ESP), like Managed Service Providers (MSP) or Cloud Service Providers (CSP).
A Document Traceability Matrix (DTM) that maps the security requirements to implemented policies, procedures, and technical controls, ensuring that all required security controls are adequately addressed and verified.
Suppose this documentation does not already exist, and an Affirming Official (AO) has entered a high compliance score in the Supplier Performance Risk System (SPRS). In that case, there has already been a False Claims Act violation, and company executives should begin discussing mitigation strategies.